View on GitHub
Open this notebook in GitHub to run it yourself
- Introduction and Problem Statement
Elliptic Curve Definition
An elliptic curve is a special type of mathematical curve defined by a cubic equation. For our purposes, we can think of it as the set of points that satisfy the Weierstrass equation: where and are constants that define the specific shape of the curve. Key Properties:- Smooth curve: The curve has no sharp corners, breaks, or self-intersections (this requires )
- Symmetric: The curve is symmetric about the x-axis - if is on the curve, then is also on the curve
- Point at infinity: We add a special “point at infinity” denoted that serves as the identity element for point addition , as will be explained in the next section.
- You can “add” any two points on the curve to get another point on the curve
- There’s an identity element () where for any point
- Every point has an inverse
- Addition is associative:
How Elliptic Curve Point Addition Works
The elliptic curve “addition” operation geometric interpretation: To add two points and on the curve, draw a straight line through them. This line will intersect the elliptic curve at exactly one more point . The sum is then defined as the reflection of across the x-axis.- Calculate a slope based on the input points
- Use to compute the x-coordinate of the result:
- Use and to compute the y-coordinate:
- Generic case: Two distinct points where
- Slope:
- Point doubling: Adding a point to itself
- Slope:
- Inverse points: (point at infinity)
- Adding point at infinity:
The Elliptic Curve Discrete Logarithm Problem (ECDLP)
Formally, an instance of the Elliptic Curve Discrete Logarithm Problem (ECDLP) is defined as follows: Let be a fixed and publicly known generator of a cyclic subgroup of with known order .Let be a fixed and publicly known element in the subgroup generated by . The problem is to find the unique integer , called the discrete logarithm, such that .
| Discrete Logarithm Problem (DLP) | Elliptic Curve DLP (ECDLP) | |
|---|---|---|
| Group operation | Modular multiplication | Modular point addition |
| Expression | Modular exponentiation: | Modular scalar multiplication: |
| Goal | Find given and | Find given and |
- A generator element ( or ) is known
- A target element ( or ) is known
- The task is to find the exponent or scalar such that the group operation applied to the generator yields the target
Real-World Impact and Applications
Cryptographic Applications:- Digital Signatures: Power cryptocurrency systems like Bitcoin and Ethereum, enabling secure ownership proofs without revealing private keys
- TLS/SSL Certificates: Use ECC-based key exchange (e.g., ECDHE) to secure HTTPS traffic across the internet
- Mobile Communications: Employ protocols such as ECDSA and ECIES for device authentication and secure messaging in 4G/5G networks
- Lightweight Cryptography: ECC is well-suited for resource-constrained environments, and is used in protocols like DTLS and TLS-PSK for IoT security
- Secure Messaging and Encryption Standards: ECC forms the basis of cryptographic protocols in standards like Suite B, used in high-security communications
- ECC-256 provides security equivalent to RSA-3072
- Smaller keys mean faster computations and less storage
- Critical for resource-constrained devices like smartphones and IoT sensors
Our Specific Example
We’ll work with a concrete example on a small finite field to demonstrate the concepts, following the approach outlined in Roetteler et al. [1]. Our specific example will demonstrate elliptic curve operations over points : Elliptic Curve: Problem: Find the discrete logarithm such that: Where:- Generator point
- Target point
- (point doubling)
- ✓
- Plus the point at infinity
- Multiples: , , , ,
- Order: (since )
- Shor’s Algorithm for ECDLP
Algorithm Overview
- Superposition Preparation: Create two quantum registers in a superposition of all possible integers between 0 and a large number
- Periodic Function Evaluation: Apply a periodic function that takes the two registers as input and computes the output in an auxiliary register
- Period Extraction: Apply an inverse Quantum Fourier Transform to reveal the hidden period of the function
The Periodic Function for Elliptic Curve
The key function evaluated in quantum superposition is: where the last equality holds by the definition of the discrete logarithm (since ). The function exhibits periodicity in both variables: where is the order of the generator . When the quantum measurement finds inputs where , the quantum Fourier transform extracts this period structure, revealing relationships that allow us to solve for the discrete logarithm . In our quantum implementation, we actually evaluate where serves as an auxiliary starting point that doesn’t affect the final discrete logarithm but helps avoid certain edge cases in the quantum arithmetic.Quantum Oracle Function Implementation
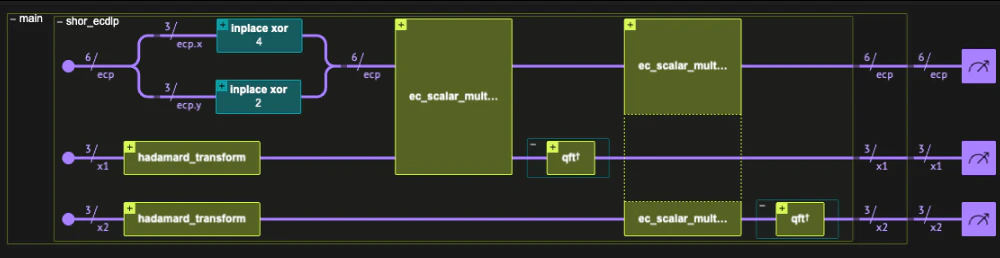
The core of our implementation is theshor_ecdlp quantum function that orchestrates the entire algorithm.
It implements the function
Expected Quantum Flow
- Initialization : All variables start in state
- State Preparation : Set initial elliptic curve point
- Superposition Creation : Apply transformation to create superposition over the possible values of and
- Quantum Arithmetic : Perform elliptic curve computation in superposition
- Period Extraction : Apply inverse QFT to extract period information
QStruct called EllipticCurvePoint to group the x and y coordinates together, making the code more organized and mathematically intuitive.
Quantum Variables:
| Variable | Purpose |
|---|---|
x1 | First quantum register for period finding (ranges 0-7) |
x2 | Second quantum register for period finding (ranges 0-7) |
ecp | Quantum elliptic curve point during computation |
| Variable | Purpose |
|---|---|
P_0 | Starting point |
G | Generator point |
P_target | Target point |
- So instead of creating the entire uniform distribution on the
x1,x2variables, we load them with the uniform superposition of only the first#GENERATOR_ORDERstates (see the “discrete log” notebook for more examples).*
prepare_uniform_trimmed_state library function, which efficiently prepares such a state.
- Quantum Elliptic Curve Addition
Algorithm Hierarchy Overview
Theshor_ecdlp function orchestrates Shor’s algorithm, but its computational core is the ec_scalar_mult_add function, which performs quantum scalar multiplication in superposition.
This function computes the expression where is in quantum superposition, enabling the algorithm to evaluate all possible scalar values simultaneously.
Quantum Scalar Multiplication (ec_scalar_mult_add)
Our implementation uses an efficient hybrid classical-quantum approach. We precompute all the powers-of-two multiples of the base point classically: .
Then we compute the scalar multiple using controlled additions of these precomputed points following the binary representation of the scalar.
Algorithm: For scalar with :
Implementation Steps:
- Classical Preprocessing: Compute powers classically
- Quantum Control: For each bit , perform controlled addition of to the accumulator
ell_double_classical function, leaving only controlled point additions for the in-place elliptic curve point addition quantum function ec_point_add.
Classical Point Doubling (ell_double_classical)
The doubling of the classically known generator is implemented as follows:
Quantum Point Addition (ec_point_add)
The ec_point_add function performs the fundamental operation of adding two elliptic curve points in a quantum-reversible manner.
Our Implementation Simplification:
Following the approach in [1], our implementation focuses only on the generic case where the two points are distinct, not inverses of each other, and neither is the neutral element.
These exceptional cases are rare (for large ) , except when the accumulation register is initialized to the neutral element.
Note: *To avoid edge cases (as described above) through the entire quantum scalar multiplication, we chose to initialize the accumulation elliptic curve point with a non-zero point () rather than the neutral element.
This strategy does not affect the measurement statistics after the Quantum Fourier Transform, since it only adds a global phase to the final quantum state. We deliberately selected a starting point that lies on the elliptic curve but is not within the subgroup generated by . Additionally, we exploited the fact that the order of is not a power of 2*
Disclaimer: This is an engineered example chosen to allow simulation of a small model where edge cases effect the results. In general, such an initialization is not always possible.
Algorithm Overview (Generic Case Only):
- Input: Quantum point and classical point
- Slope calculation: Compute using quantum modular inverse
- Result coordinates:
- Cleanup: Uncompute auxiliary values to maintain reversibility
ec_point_add function is based on Algorithm 1 from “Quantum resource estimates for computing elliptic curve discrete logarithms” by Roetteler et al. (2017) [1]
To implement ec_point_add, we need a complete library of reversible modular arithmetic operations which we import directly from the Classiq open library.
Modular Arithmetic Functions imported from Classiq Open Library
- Organized by Category:
-
modular_add_inplace - Modular addition
-
modular_negate_inplace - Modular negation
-
modular_subtract_inplace - Modular subtraction
-
modular_add_constant_inplace - Modular addition of a classical constant
-
modular_multiply - Modular multiplication
-
modular_square - Modular squaring
mock_modular_inverse based on a classical lookup table specifically for modulo 7, instead of implementing the full quantum modular inversion function modular_inverse_inplace (based on “Kaliski’s algorithm”), which requires significant qubit resources.
*The above choice is driven by the practical desire to first fully simulate the entire elliptic curve discrete logarithm (ECDLP) algorithm flow within the limits of currently available quantum simulators.
The full ECDLP synthesized circuit (including the full modular_inverse_inplace implementation) is presented at the end of this notebook.*
ec_point_add) from the output point and the known input using the identity:
This ensures that can be safely overwritten with while still allowing recovery of for uncomputing it.
Step-by-Step Point Addition Example
Let’s see how elliptic curve point addition actually works by computing : Step 1: Calculate the slope For two distinct points and : Note: , and since Actually: Step 2: Calculate the x-coordinate of the result Step 3: Calculate the y-coordinate of the result Result: Lets applyec_point_add to add and :
Output:
Output:
- Execute the Entire Algorithm Flow
shor_ecdlp function.
Main function
Model creation and synthesis
Output:
Quantum Program Analysis
We can analyze the transpiled circuit characteristics from the quantum program object:Output:
Output:
Execution
Results Collection
Output:
- Post-Processing Results
| x1 | x2 | ecp.x | ecp.y | count | probability | bitstring | x1_rounded | x2_rounded | |
|---|---|---|---|---|---|---|---|---|---|
| 0 | 0.000 | 0.000 | 3 | 2 | 100 | 0.048828 | 010011000000 | 0.0 | 0.0 |
| 1 | 0.000 | 0.000 | 5 | 0 | 95 | 0.046387 | 000101000000 | 0.0 | 0.0 |
| 2 | 0.375 | 0.375 | 3 | 2 | 87 | 0.042480 | 010011011011 | 2.0 | 2.0 |
| 3 | 0.625 | 0.625 | 3 | 2 | 83 | 0.040527 | 010011101101 | 3.0 | 3.0 |
| 4 | 0.000 | 0.000 | 4 | 5 | 82 | 0.040039 | 101100000000 | 0.0 | 0.0 |
| 5 | 0.625 | 0.625 | 5 | 0 | 77 | 0.037598 | 000101101101 | 3.0 | 3.0 |
| 6 | 0.375 | 0.375 | 5 | 0 | 71 | 0.034668 | 000101011011 | 2.0 | 2.0 |
| 7 | 0.000 | 0.000 | 4 | 2 | 71 | 0.034668 | 010100000000 | 0.0 | 0.0 |
| 8 | 0.000 | 0.000 | 3 | 5 | 69 | 0.033691 | 101011000000 | 0.0 | 0.0 |
| 9 | 0.625 | 0.625 | 3 | 5 | 61 | 0.029785 | 101011101101 | 3.0 | 3.0 |
x2 is co-prime to the order, such that we can get the logarithm by multiplying x1 by the modular inverse. If the x1, x2 registers are large enough, we are guaranteed to sample it with a good probability.
From the valid solutions, we solve for the discrete logarithm using:
| x1 | x2 | ecp.x | ecp.y | count | probability | bitstring | x1_rounded | x2_rounded | x2_inverse | logarithm | |
|---|---|---|---|---|---|---|---|---|---|---|---|
| 2 | 0.375 | 0.375 | 3 | 2 | 87 | 0.042480 | 010011011011 | 2.0 | 2.0 | 3 | 4.0 |
| 3 | 0.625 | 0.625 | 3 | 2 | 83 | 0.040527 | 010011101101 | 3.0 | 3.0 | 2 | 4.0 |
| 5 | 0.625 | 0.625 | 5 | 0 | 77 | 0.037598 | 000101101101 | 3.0 | 3.0 | 2 | 4.0 |
| 6 | 0.375 | 0.375 | 5 | 0 | 71 | 0.034668 | 000101011011 | 2.0 | 2.0 | 3 | 4.0 |
| 9 | 0.625 | 0.625 | 3 | 5 | 61 | 0.029785 | 101011101101 | 3.0 | 3.0 | 2 | 4.0 |
| 10 | 0.375 | 0.375 | 4 | 5 | 59 | 0.028809 | 101100011011 | 2.0 | 2.0 | 3 | 4.0 |
| 11 | 0.625 | 0.625 | 4 | 5 | 59 | 0.028809 | 101100101101 | 3.0 | 3.0 | 2 | 4.0 |
| 12 | 0.375 | 0.375 | 3 | 5 | 58 | 0.028320 | 101011011011 | 2.0 | 2.0 | 3 | 4.0 |
| 13 | 0.375 | 0.375 | 4 | 2 | 56 | 0.027344 | 010100011011 | 2.0 | 2.0 | 3 | 4.0 |
| 14 | 0.625 | 0.625 | 4 | 2 | 52 | 0.025391 | 010100101101 | 3.0 | 3.0 | 2 | 4.0 |
Quantum Algorithm Success
The fact that multiple valid pairs yield the same discrete logarithm (l = 4) confirms the quantum algorithm worked correctly, extracting the hidden period structure from Shor’s algorithm.
- The Full Quantum Elliptic Curve Addition Quantum Program
ec_point_add using the quantum modular inversion function modular_inverse_inplace (based on “Kaliski’s algorithm”) - imported directly from the Classiq Open Library.
Output:
- The Full ECDLP Quantum Program
Output:

